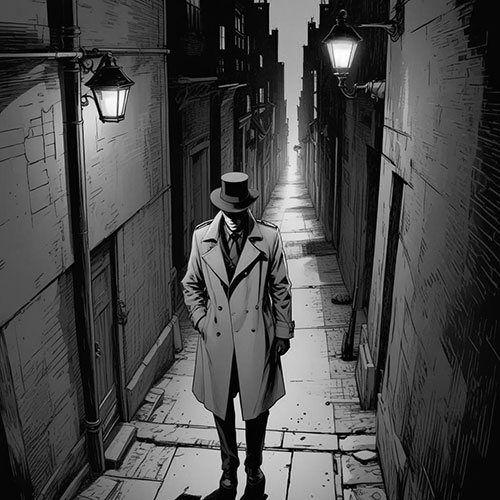
Agents, are deployed to the heart of West Berlin, a city pulsing with Cold War tension, to undertake a covert operation at the Belevot Hotel—a faded Art Deco gem near Kurfrstendamm, its neon lights casting an eerie glow on rain-slicked cobblestones. Your targets are Vaclav Kopecky, the notorious Prague Broker, and the shadowy figure known only as the Shadow Wolf. Be warned: an unexpected threat, a rival hitman, may throw your plans into disarray. The stakes are high, and the fate of nations hangs in the balance. Proceed with utmost secrecy.
Your mission begins with infiltrating Suite 804, the lavish domain of Vaclav Kopecky—a fat, charming yet ruthless arms dealer with a taste for opulence, draped in tailored suits, adorned with a gold watch, and arriving in a sleek black luxury sedan. He is a man haunted by paranoia, always suspecting the watchful eyes of the KGB or CIA, and he moves with extreme caution. Between 9:00 PM and 10:30 PM, while he attends an underground card game in the basement casino, you must slip into his suite. There, you will find a leather-bound dossier sealed with a Cyrillic mark and a locked metal case holding mysterious samples—items tied to a secretive Soviet project. Your task is to photograph every page of the dossier and capture images of the case, leaving no trace of your presence, as Kopecky is guarded by three fiercely loyal bodyguards: - Boris "The Bear" Volkov, a towering ex-Spetsnaz soldier with a scarred face, a silent enforcer who watches every corner. - Elena "Whisper" Sokolova, a sharp-featured ex-Stasi operative, ever-vigilant with a keen eye for deception. - Mikhail "Sly" Petrov, a wiry ex-KGB driver with a quick draw and a love for the casino’s thrills. One of these guards will remain in the suite, patrolling with unwavering focus.
While in Suite 804 during the earlier window, you must plant a hidden audio bug to capture a critical meeting. At 3:00 AM, Kopecky will hand over the mysterious materials to the Shadow Wolf, a figure shrouded in mystery, linked to daring crimes like the Buenos Aires Artifact Heist, the Lisbon Incident, and the Vienna Cipher Murders. From the safety of your nearby hotel room, you will listen live and record this exchange, hoping to capture the Shadow Wolf’s voice—a clue that may unravel their connection to a project called ‘Fenrir,’ hinted at in the dossier’s pages. Take every precaution to avoid detection by the bodyguards or the Shadow Wolf’s own watchful eyes.
 Belevont Hotel
Belevont HotelBerlin, Germany
Daniel Kessler
IRON VEIL
CODENAME: Ebony Shroud
 Vaclav Kopecky
Vaclav KopeckyBlack-Market Arms Dealer
Born in Prague during the post-war Soviet occupation, Vaclav rose from a modest family to become a key figure in the underground arms trade. A former logistics officer in the Czechoslovak People’s Army, he defected in 1975 after uncovering a corrupt deal, using his connections to establish a lucrative black-market empire in West Berlin. His wealth—earned from selling weapons and stolen tech to the highest bidders—funds a lavish lifestyle, including a black Mercedes-Benz 500SEL and a penthouse suite at the Belevot Hotel.
 The Shadow Wolf
The Shadow WolfUNKNOWN
The Shadow Wolf is a phantom figure whose origins remain shrouded in secrecy, first emerging on intelligence radar with the audacious Buenos Aires Artifact Heist in 1981, where a Nazi-era relic vanished without a trace, marked only by a wolf’s head symbol etched at the scene. Their trail continued with the Lisbon Incident in 1983, a daring theft of classified Soviet documents, and peaked with the Vienna Cipher Murders later that year, where three cryptographers were silently eliminated, again leaving the same cryptic symbol. Operating with unmatched stealth and leaving behind only whispers and that elusive symbol, the Shadow Wolf is believed to be meeting Vaclav Kopecky at the Belevot Hotel on July 17, 1984, to acquire materials that could unlock their next enigmatic move.
 Boris Volkov
Boris VolkovMuscle and Enforcer
 Elena Sokolova
Elena SokolovaSurveillance and Intelligence
 Mikhail Petrov
Mikhail PetrovDriver and Quick-Draw
 Belevot Hotel
Belevot HotelWest Berlin, Germany
Daniel Kessler - Hawk
Participating Agents:
Helga Schneider - Eisenkrypt
Ezekiel Hawthorne - The Professor
- Agent Arrive at Belevont Hotel
- Kopecky arrives by private plane.
- Kopecky checks into Suite 804 with his bodyguards.
- Kopecky joins the casino game
- Kopecky returns to Room and waits for Meeting
- The handoff with the Shadow Wolf takes place in Suite 804.
IRON VEIL